Vulnerability Scan Result

| ip_address | 77.72.134.146 |
| country | DE |
| network_name | Colobridge GMBH |
| asn | AS197252 |
21/tcp | ftp | ProFTPD - |
25/tcp | smtp | Exim smtpd 4.95 |
53/tcp | domain | ISC BIND 9.18.30-0ubuntu0.22.04.2 |
80/tcp | http | Apache httpd 2.4.52 |
110/tcp | pop3 | Dovecot pop3d - |
143/tcp | imap | Dovecot imapd - |
443/tcp | https | Apache httpd 2.4.52 |
465/tcp | smtp | Exim smtpd 4.95 |
587/tcp | smtp | Exim smtpd 4.95 |
993/tcp | imap | Dovecot imapd - |
995/tcp | pop3 | Dovecot pop3d - |
No technologies could be detected.
Web Application Vulnerabilities
Evidence
| URL | Evidence |
|---|---|
| https://club.vladimirzakharov.com/ | Response headers do not include the X-Content-Type-Options HTTP security header |
Vulnerability description
We noticed that the target application's server responses lack the X-Content-Type-Options header. This header is particularly important for preventing Internet Explorer from reinterpreting the content of a web page (MIME-sniffing) and thus overriding the value of the Content-Type header.
Risk description
The risk is that lack of this header could make possible attacks such as Cross-Site Scripting or phishing in Internet Explorer browsers.
Recommendation
We recommend setting the X-Content-Type-Options header such as `X-Content-Type-Options: nosniff`.
Classification
| CWE | CWE-693 |
| OWASP Top 10 - 2017 | |
| OWASP Top 10 - 2021 |
Evidence
| URL | Evidence |
|---|---|
| https://club.vladimirzakharov.com/ | Response does not include the HTTP Content-Security-Policy security header or meta tag |
Vulnerability description
We noticed that the target application lacks the Content-Security-Policy (CSP) header in its HTTP responses. The CSP header is a security measure that instructs web browsers to enforce specific security rules, effectively preventing the exploitation of Cross-Site Scripting (XSS) vulnerabilities.
Risk description
The risk is that if the target application is vulnerable to XSS, lack of this header makes it easily exploitable by attackers.
Recommendation
Configure the Content-Security-Header to be sent with each HTTP response in order to apply the specific policies needed by the application.
Classification
| CWE | CWE-693 |
| OWASP Top 10 - 2017 | |
| OWASP Top 10 - 2021 |
Evidence
| URL | Method | Parameters | Evidence |
|---|---|---|---|
| https://club.vladimirzakharov.com/ | GET | Query: goal=0_4715aa5204-2cb334a784-283233456 mc_cid=2cb334a784 mc_eid=UNIQID utm_campaign=2cb334a784-EMAIL_CAMPAIGN_2019_03_20_08_08_COPY_01 utm_medium=email utm_source=Активные подписчики utm_term=0_4715aa5204-2cb334a784-283233456 Headers: User-Agent=Mozilla/5.0 (Windows NT 10.0; ... |
|
Vulnerability description
We noticed that the target application is serving mixed content. This occurs when initial HTML is loaded over a secure HTTPS connection, but other resources (such as images, videos, stylesheets, scripts) are loaded over an insecure HTTP connection. This is called mixed content because both HTTP and HTTPS content are being loaded to display the same page, and the initial request was secure over HTTPS.
Risk description
The risk is that the insecurely loaded resources (HTTP) on an otherwise secure page (HTTPS) can be intercepted or manipulated by attackers, potentially leading to eavesdropping or content tampering.
Recommendation
Ensure that all external resources the page references are loaded using HTTPS.
Classification
| CWE | CWE-311 |
| OWASP Top 10 - 2017 | |
| OWASP Top 10 - 2021 |
Evidence
| URL | Evidence |
|---|---|
| https://club.vladimirzakharov.com/ | Response headers do not include the Referrer-Policy HTTP security header as well as the |
Vulnerability description
We noticed that the target application's server responses lack the Referrer-Policy HTTP header, which controls how much referrer information the browser will send with each request originated from the current web application.
Risk description
The risk is that if a user visits a web page (e.g. "http://example.com/pricing/") and clicks on a link from that page going to e.g. "https://www.google.com", the browser will send to Google the full originating URL in the `Referer` header, assuming the Referrer-Policy header is not set. The originating URL could be considered sensitive information and it could be used for user tracking.
Recommendation
The Referrer-Policy header should be configured on the server side to avoid user tracking and inadvertent information leakage. The value `no-referrer` of this header instructs the browser to omit the Referer header entirely.
Classification
| CWE | CWE-693 |
| OWASP Top 10 - 2017 | |
| OWASP Top 10 - 2021 |
Evidence
Vulnerability description
We found the robots.txt on the target server. This file instructs web crawlers what URLs and endpoints of the web application they can visit and crawl. Website administrators often misuse this file while attempting to hide some web pages from the users.
Risk description
There is no particular security risk in having a robots.txt file. However, it's important to note that adding endpoints in it should not be considered a security measure, as this file can be directly accessed and read by anyone.
Recommendation
We recommend you to manually review the entries from robots.txt and remove the ones which lead to sensitive locations in the website (ex. administration panels, configuration files, etc).
Evidence
Vulnerability description
Website is accessible.
Vulnerability description
We have noticed that the server is missing the security.txt file, which is considered a good practice for web security. It provides a standardized way for security researchers and the public to report security vulnerabilities or concerns by outlining the preferred method of contact and reporting procedures.
Risk description
There is no particular risk in not having a security.txt file for your server. However, this file is important because it offers a designated channel for reporting vulnerabilities and security issues.
Recommendation
We recommend you to implement the security.txt file according to the standard, in order to allow researchers or users report any security issues they find, improving the defensive mechanisms of your server.
Evidence
| URL | Evidence |
|---|---|
| https://club.vladimirzakharov.com/ |
|
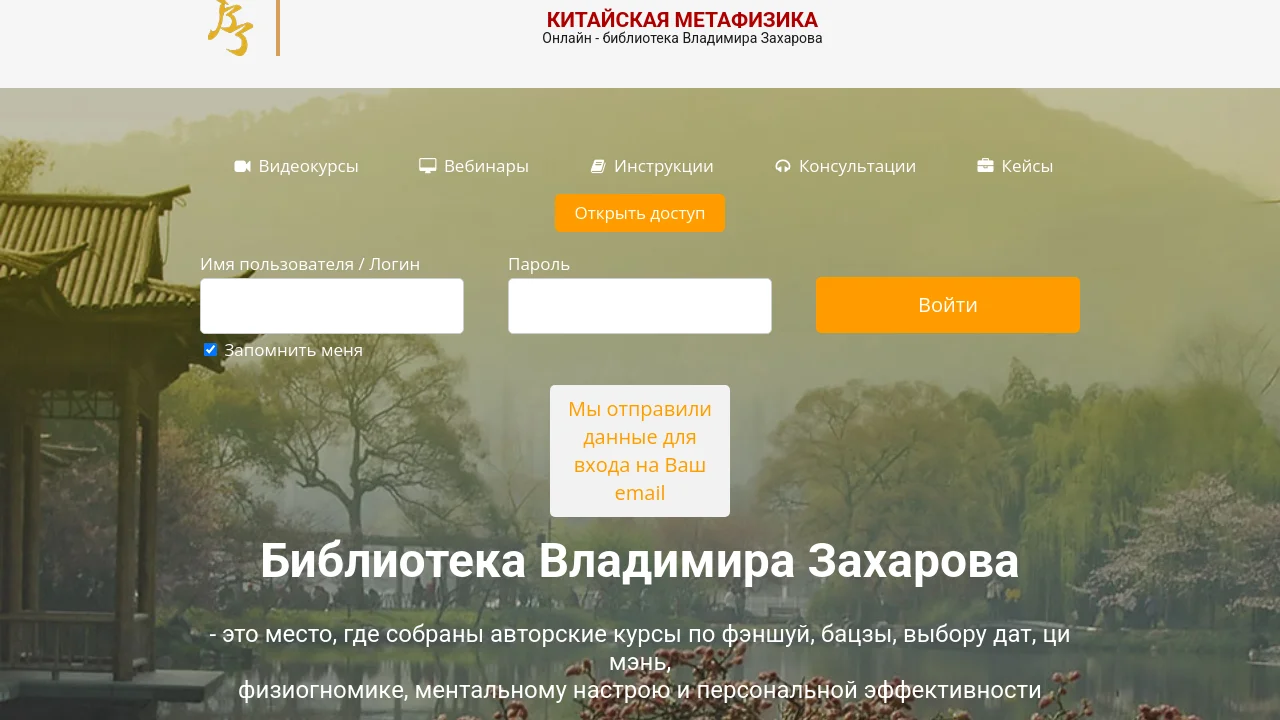
Vulnerability description
We have discovered that the target application presents a login interface that could be a potential target for attacks. While login interfaces are standard for user authentication, they can become vulnerabilities if not properly secured.
Risk description
The risk is that an attacker could use this interface to mount brute force attacks against known passwords and usernames combinations leaked throughout the web.
Recommendation
Ensure each interface is not bypassable using common knowledge of the application or leaked credentials using occasional password audits.
Evidence
| URL | Method | Parameters | Evidence |
|---|---|---|---|
| https://club.vladimirzakharov.com/wp-json/oembed/1.0/embed | GET | Query: format=xml url=https://club.vladimirzakharov.com/ Headers: User-Agent=Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36 Cookies: PHPSESSID=0859ebd9f494275933b6064f86caccbe wordpress_test_cookie=WP+Cookie+check | Possible API endpoint found at |
| https://club.vladimirzakharov.com/wp-json/oembed/1.0/embed | GET | Query: url=https://club.vladimirzakharov.com/ Headers: User-Agent=Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36 Cookies: PHPSESSID=0859ebd9f494275933b6064f86caccbe wordpress_test_cookie=WP+Cookie+check | Possible API endpoint found at |
Vulnerability description
We found API endpoints while crawling the given web application.
Risk description
These endpoints may represent an attack surface for malicious actors interested in API-specific vulnerabilities.
Recommendation
Use the API Scanner to perform a more thorough vulnerability check for these endpoints, if an API specification is present.
Evidence
| URL | Method | Parameters | Evidence |
|---|---|---|---|
| https://club.vladimirzakharov.com/ | GET | Query: goal=0_4715aa5204-2cb334a784-283233456 mc_cid=2cb334a784 mc_eid=UNIQID utm_campaign=2cb334a784-EMAIL_CAMPAIGN_2019_03_20_08_08_COPY_01 utm_medium=email utm_source=Активные подписчики utm_term=0_4715aa5204-2cb334a784-283233456 Headers: User-Agent=Mozilla/5.0 (Windows NT 10.0; ... | Email Address: fengshuicourses@gmail.com |
Vulnerability description
We noticed that this web application exposes email addresses, which might be unintended. While not inherently a vulnerability, this information could be leveraged in social engineering or spam related activities.
Risk description
The risk is that exposed email addresses within the application could be accessed by unauthorized parties. This could lead to privacy violations, spam, phishing attacks, or other forms of misuse.
Recommendation
Compartmentalize the application to have 'safe' areas where trust boundaries can be unambiguously drawn. Do not allow email addresses to go outside of the trust boundary, and always be careful when interfacing with a compartment outside of the safe area.
Classification
| CWE | CWE-200 |
| OWASP Top 10 - 2017 | |
| OWASP Top 10 - 2021 |
Infrastructure Vulnerabilities
Evidence
| CVE | CVSS | EPSS Score | EPSS Percentile | CISA KEV | Summary |
|---|---|---|---|---|---|
| CVE-2024-38476 | 9.8 | 0.01393 | 0.79521 | No | Vulnerability in core of Apache HTTP Server 2.4.59 and earlier are vulnerably to information disclosure, SSRF or local script execution via backend applications whose response headers are malicious or exploitable. Users are recommended to upgrade to version 2.4.60, which fixes this issue. |
| CVE-2024-38474 | 9.8 | 0.00764 | 0.72438 | No | Substitution encoding issue in mod_rewrite in Apache HTTP Server 2.4.59 and earlier allows attacker to execute scripts in directories permitted by the configuration but not directly reachable by any URL or source disclosure of scripts meant to only to be executed as CGI. Users are recommended to upgrade to version 2.4.60, which fixes this issue. Some RewriteRules that capture and substitute unsafely will now fail unless rewrite flag "UnsafeAllow3F" is specified. |
| CVE-2023-25690 | 9.8 | 0.73308 | 0.98714 | No | Some mod_proxy configurations on Apache HTTP Server versions 2.4.0 through 2.4.55 allow a HTTP Request Smuggling attack. Configurations are affected when mod_proxy is enabled along with some form of RewriteRule or ProxyPassMatch in which a non-specific pattern matches some portion of the user-supplied request-target (URL) data and is then re-inserted into the proxied request-target using variable substitution. For example, something like: RewriteEngine on RewriteRule "^/here/(.*)" "http://example.com:8080/elsewhere?$1"; [P] ProxyPassReverse /here/ http://example.com:8080/ Request splitting/smuggling could result in bypass of access controls in the proxy server, proxying unintended URLs to existing origin servers, and cache poisoning. Users are recommended to update to at least version 2.4.56 of Apache HTTP Server. |
| CVE-2024-38475 | 9.1 | 0.9355 | 0.99825 | Yes | Improper escaping of output in mod_rewrite in Apache HTTP Server 2.4.59 and earlier allows an attacker to map URLs to filesystem locations that are permitted to be served by the server but are not intentionally/directly reachable by any URL, resulting in code execution or source code disclosure. Substitutions in server context that use a backreferences or variables as the first segment of the substitution are affected. Some unsafe RewiteRules will be broken by this change and the rewrite flag "UnsafePrefixStat" can be used to opt back in once ensuring the substitution is appropriately constrained. |
| CVE-2022-36760 | 9 | 0.00295 | 0.52393 | No | Inconsistent Interpretation of HTTP Requests ('HTTP Request Smuggling') vulnerability in mod_proxy_ajp of Apache HTTP Server allows an attacker to smuggle requests to the AJP server it forwards requests to. This issue affects Apache HTTP Server Apache HTTP Server 2.4 version 2.4.54 and prior versions. |
Vulnerability description
Vulnerabilities found for Apache HTTP Server 2.4.52
Risk description
These vulnerabilities expose the affected applications to the risk of unauthorized access to confidential data and possibly to denial of service attacks. An attacker could search for an appropriate exploit (or create one) for any of these vulnerabilities and use it to attack the system. Notes: - The vulnerabilities are identified based on the server's version.; - Only the first 5 vulnerabilities with the highest risk are shown for each port.; Since the vulnerabilities were discovered using only version-based testing, the risk level for this finding will not exceed "high" severity. Critical risks will be assigned to vulnerabilities identified through accurate active testing methods.
Recommendation
We recommend you to upgrade the affected software to the latest version in order to eliminate the risks imposed by these vulnerabilities.
Evidence
| CVE | CVSS | EPSS Score | EPSS Percentile | CISA KEV | Summary |
|---|---|---|---|---|---|
| CVE-2022-37451 | 7.5 | 0.03872 | 0.87733 | No | Exim before 4.96 has an invalid free in pam_converse in auths/call_pam.c because store_free is not used after store_malloc. |
| CVE-2022-3620 | 5.6 | 0.00275 | 0.50599 | No | A vulnerability was found in Exim and classified as problematic. This issue affects the function dmarc_dns_lookup of the file dmarc.c of the component DMARC Handler. The manipulation leads to use after free. The attack may be initiated remotely. The name of the patch is 12fb3842f81bcbd4a4519d5728f2d7e0e3ca1445. It is recommended to apply a patch to fix this issue. The associated identifier of this vulnerability is VDB-211919. |
| CVE-2024-39929 | 5.4 | 0.39994 | 0.97168 | No | Exim through 4.97.1 misparses a multiline RFC 2231 header filename, and thus remote attackers can bypass a $mime_filename extension-blocking protection mechanism, and potentially deliver executable attachments to the mailboxes of end users. |
| CVE-2023-51766 | 5.3 | 0.03209 | 0.86488 | No | Exim before 4.97.1 allows SMTP smuggling in certain PIPELINING/CHUNKING configurations. Remote attackers can use a published exploitation technique to inject e-mail messages with a spoofed MAIL FROM address, allowing bypass of an SPF protection mechanism. This occurs because Exim supports <LF>.<CR><LF> but some other popular e-mail servers do not. |
| CVE-2022-3559 | 4.6 | 0.00169 | 0.38802 | No | A vulnerability was found in Exim and classified as problematic. This issue affects some unknown processing of the component Regex Handler. The manipulation leads to use after free. The name of the patch is 4e9ed49f8f12eb331b29bd5b6dc3693c520fddc2. It is recommended to apply a patch to fix this issue. The identifier VDB-211073 was assigned to this vulnerability. |
Vulnerability description
Vulnerabilities found for Exim Smtpd 4.95
Risk description
These vulnerabilities expose the affected applications to the risk of unauthorized access to confidential data and possibly to denial of service attacks. An attacker could search for an appropriate exploit (or create one) for any of these vulnerabilities and use it to attack the system. Notes: - The vulnerabilities are identified based on the server's version.; - Only the first 5 vulnerabilities with the highest risk are shown for each port.; Since the vulnerabilities were discovered using only version-based testing, the risk level for this finding will not exceed "high" severity. Critical risks will be assigned to vulnerabilities identified through accurate active testing methods.
Recommendation
We recommend you to upgrade the affected software to the latest version in order to eliminate the risks imposed by these vulnerabilities.
Evidence
| CVE | CVSS | EPSS Score | EPSS Percentile | CISA KEV | Summary |
|---|---|---|---|---|---|
| CVE-2020-28035 | 7.5 | 0.04877 | 0.89096 | No | WordPress before 5.5.2 allows attackers to gain privileges via XML-RPC. |
| CVE-2020-28032 | 7.5 | 0.20723 | 0.95319 | No | WordPress before 5.5.2 mishandles deserialization requests in wp-includes/Requests/Utility/FilteredIterator.php. |
| CVE-2019-20041 | 7.5 | 0.02395 | 0.84363 | No | wp_kses_bad_protocol in wp-includes/kses.php in WordPress before 5.3.1 mishandles the HTML5 colon named entity, allowing attackers to bypass input sanitization, as demonstrated by the javascript: substring. |
| CVE-2019-17670 | 7.5 | 0.04761 | 0.88965 | No | WordPress before 5.2.4 has a Server Side Request Forgery (SSRF) vulnerability because Windows paths are mishandled during certain validation of relative URLs. |
| CVE-2019-17669 | 7.5 | 0.11017 | 0.93105 | No | WordPress before 5.2.4 has a Server Side Request Forgery (SSRF) vulnerability because URL validation does not consider the interpretation of a name as a series of hex characters. |
Vulnerability description
Vulnerabilities found for WordPress 4.9.15
Risk description
These vulnerabilities expose the affected applications to the risk of unauthorized access to confidential data and possibly to denial of service attacks. An attacker could search for an appropriate exploit (or create one) for any of these vulnerabilities and use it to attack the system. Notes: - The vulnerabilities are identified based on the server's version.; - Only the first 5 vulnerabilities with the highest risk are shown for each port.; Since the vulnerabilities were discovered using only version-based testing, the risk level for this finding will not exceed "high" severity. Critical risks will be assigned to vulnerabilities identified through accurate active testing methods.
Recommendation
We recommend you to upgrade the affected software to the latest version in order to eliminate the risks imposed by these vulnerabilities.
Evidence
| CVE | CVSS | EPSS Score | EPSS Percentile | CISA KEV | Summary |
|---|---|---|---|---|---|
| CVE-2022-37451 | 7.5 | 0.03872 | 0.87733 | No | Exim before 4.96 has an invalid free in pam_converse in auths/call_pam.c because store_free is not used after store_malloc. |
| CVE-2022-3620 | 5.6 | 0.00275 | 0.50599 | No | A vulnerability was found in Exim and classified as problematic. This issue affects the function dmarc_dns_lookup of the file dmarc.c of the component DMARC Handler. The manipulation leads to use after free. The attack may be initiated remotely. The name of the patch is 12fb3842f81bcbd4a4519d5728f2d7e0e3ca1445. It is recommended to apply a patch to fix this issue. The associated identifier of this vulnerability is VDB-211919. |
| CVE-2024-39929 | 5.4 | 0.39994 | 0.97168 | No | Exim through 4.97.1 misparses a multiline RFC 2231 header filename, and thus remote attackers can bypass a $mime_filename extension-blocking protection mechanism, and potentially deliver executable attachments to the mailboxes of end users. |
| CVE-2023-51766 | 5.3 | 0.03209 | 0.86488 | No | Exim before 4.97.1 allows SMTP smuggling in certain PIPELINING/CHUNKING configurations. Remote attackers can use a published exploitation technique to inject e-mail messages with a spoofed MAIL FROM address, allowing bypass of an SPF protection mechanism. This occurs because Exim supports <LF>.<CR><LF> but some other popular e-mail servers do not. |
| CVE-2022-3559 | 4.6 | 0.00169 | 0.38802 | No | A vulnerability was found in Exim and classified as problematic. This issue affects some unknown processing of the component Regex Handler. The manipulation leads to use after free. The name of the patch is 4e9ed49f8f12eb331b29bd5b6dc3693c520fddc2. It is recommended to apply a patch to fix this issue. The identifier VDB-211073 was assigned to this vulnerability. |
Vulnerability description
Vulnerabilities found for Exim Smtpd 4.95
Risk description
These vulnerabilities expose the affected applications to the risk of unauthorized access to confidential data and possibly to denial of service attacks. An attacker could search for an appropriate exploit (or create one) for any of these vulnerabilities and use it to attack the system. Notes: - The vulnerabilities are identified based on the server's version.; - Only the first 5 vulnerabilities with the highest risk are shown for each port.; Since the vulnerabilities were discovered using only version-based testing, the risk level for this finding will not exceed "high" severity. Critical risks will be assigned to vulnerabilities identified through accurate active testing methods.
Recommendation
We recommend you to upgrade the affected software to the latest version in order to eliminate the risks imposed by these vulnerabilities.
Evidence
| CVE | CVSS | EPSS Score | EPSS Percentile | CISA KEV | Summary |
|---|---|---|---|---|---|
| CVE-2022-37451 | 7.5 | 0.03872 | 0.87733 | No | Exim before 4.96 has an invalid free in pam_converse in auths/call_pam.c because store_free is not used after store_malloc. |
| CVE-2022-3620 | 5.6 | 0.00275 | 0.50599 | No | A vulnerability was found in Exim and classified as problematic. This issue affects the function dmarc_dns_lookup of the file dmarc.c of the component DMARC Handler. The manipulation leads to use after free. The attack may be initiated remotely. The name of the patch is 12fb3842f81bcbd4a4519d5728f2d7e0e3ca1445. It is recommended to apply a patch to fix this issue. The associated identifier of this vulnerability is VDB-211919. |
| CVE-2024-39929 | 5.4 | 0.39994 | 0.97168 | No | Exim through 4.97.1 misparses a multiline RFC 2231 header filename, and thus remote attackers can bypass a $mime_filename extension-blocking protection mechanism, and potentially deliver executable attachments to the mailboxes of end users. |
| CVE-2023-51766 | 5.3 | 0.03209 | 0.86488 | No | Exim before 4.97.1 allows SMTP smuggling in certain PIPELINING/CHUNKING configurations. Remote attackers can use a published exploitation technique to inject e-mail messages with a spoofed MAIL FROM address, allowing bypass of an SPF protection mechanism. This occurs because Exim supports <LF>.<CR><LF> but some other popular e-mail servers do not. |
| CVE-2022-3559 | 4.6 | 0.00169 | 0.38802 | No | A vulnerability was found in Exim and classified as problematic. This issue affects some unknown processing of the component Regex Handler. The manipulation leads to use after free. The name of the patch is 4e9ed49f8f12eb331b29bd5b6dc3693c520fddc2. It is recommended to apply a patch to fix this issue. The identifier VDB-211073 was assigned to this vulnerability. |
Vulnerability description
Vulnerabilities found for Exim Smtpd 4.95
Risk description
These vulnerabilities expose the affected applications to the risk of unauthorized access to confidential data and possibly to denial of service attacks. An attacker could search for an appropriate exploit (or create one) for any of these vulnerabilities and use it to attack the system. Notes: - The vulnerabilities are identified based on the server's version.; - Only the first 5 vulnerabilities with the highest risk are shown for each port.; Since the vulnerabilities were discovered using only version-based testing, the risk level for this finding will not exceed "high" severity. Critical risks will be assigned to vulnerabilities identified through accurate active testing methods.
Recommendation
We recommend you to upgrade the affected software to the latest version in order to eliminate the risks imposed by these vulnerabilities.
Evidence
| CVE | CVSS | EPSS Score | EPSS Percentile | CISA KEV | Summary |
|---|---|---|---|---|---|
| CVE-2019-20891 | 6.8 | 0.0013 | 0.33404 | No | WooCommerce before 3.6.5, when it handles CSV imports of products, has a cross-site request forgery (CSRF) issue with resultant stored cross-site scripting (XSS) via includes/admin/importers/class-wc-product-csv-importer-controller.php. |
| CVE-2025-5062 | 6.1 | 0.00184 | 0.40602 | No | The WooCommerce plugin for WordPress is vulnerable to PostMessage-Based Cross-Site Scripting via the 'customize-store' page in all versions up to, and including, 9.4.2 due to insufficient input sanitization and output escaping on PostMessage data. This makes it possible for unauthenticated attackers to inject arbitrary web scripts in pages that execute if they can successfully trick a user into performing an action such as clicking on a link. |
| CVE-2024-9944 | 5.3 | 0.00145 | 0.35691 | No | The WooCommerce plugin for WordPress is vulnerable to HTML Injection in all versions up to, and including, 9.0.2. This is due to the plugin not properly neutralizing HTML elements from submitted order forms. This makes it possible for unauthenticated attackers to inject arbitrary HTML that will render when the administrator views order form submissions. |
| CVE-2020-29156 | 5 | 0.13078 | 0.93764 | No | The WooCommerce plugin before 4.7.0 for WordPress allows remote attackers to view the status of arbitrary orders via the order_id parameter in a fetch_order_status action. |
| CVE-2019-9168 | 4.3 | 0.00192 | 0.41538 | No | WooCommerce before 3.5.5 allows XSS via a Photoswipe caption. |
Vulnerability description
Vulnerabilities found for WooCommerce 3.4.8
Risk description
These vulnerabilities expose the affected applications to the risk of unauthorized access to confidential data and possibly to denial of service attacks. An attacker could search for an appropriate exploit (or create one) for any of these vulnerabilities and use it to attack the system. Notes: - The vulnerabilities are identified based on the server's version.; - Only the first 5 vulnerabilities with the highest risk are shown for each port.; Since the vulnerabilities were discovered using only version-based testing, the risk level for this finding will not exceed "high" severity. Critical risks will be assigned to vulnerabilities identified through accurate active testing methods.
Recommendation
We recommend you to upgrade the affected software to the latest version in order to eliminate the risks imposed by these vulnerabilities.
Evidence
We managed to detect that Exim smtpd has reached the End-of-Life (EOL).
Version detected: 4.95 End-of-life date: 2022-06-25 Latest version for the cycle: 4.95 This release cycle (4.95) doesn't have long-term-support (LTS). The cycle was released on 2021-09-28 and its latest release date was 2021-09-28.
Risk description
Using end-of-life (EOL) software poses significant security risks for organizations. EOL software no longer receives updates, including critical security patches. This creates a vulnerability landscape where known and potentially new security flaws remain unaddressed, making the software an attractive target for malicious actors. Attackers can exploit these vulnerabilities to gain unauthorized access, disrupt services, or steal sensitive data. Moreover, without updates, compatibility issues arise with newer technologies, leading to operational inefficiencies and increased potential for system failures. Additionally, regulatory and compliance risks accompany the use of EOL software. Many industries have strict data protection regulations that require up-to-date software to ensure the highest security standards. Non-compliance can result in hefty fines and legal consequences. Organizations also risk damaging their reputation if a breach occurs due to outdated software, eroding customer trust and potentially leading to a loss of business. Therefore, continuing to use EOL software undermines both security posture and business integrity, necessitating timely upgrades and proactive risk management strategies.
Recommendation
To mitigate the risks associated with end-of-life (EOL) software, it's crucial to take proactive steps. Start by identifying any EOL software currently in use within your organization. Once identified, prioritize upgrading or replacing these applications with supported versions that receive regular updates and security patches. This not only helps close security gaps but also ensures better compatibility with newer technologies, enhancing overall system efficiency and reliability.Additionally, develop a comprehensive software lifecycle management plan. This plan should include regular audits to identify upcoming EOL dates and a schedule for timely updates or replacements. Train your IT staff and users about the importance of keeping software up to date and the risks associated with using outdated versions. By maintaining a proactive approach to software management, you can significantly reduce security risks, ensure compliance with industry regulations, and protect your organization's reputation and customer trust.
Evidence
We managed to detect that Exim smtpd has reached the End-of-Life (EOL).
Version detected: 4.95 End-of-life date: 2022-06-25 Latest version for the cycle: 4.95 This release cycle (4.95) doesn't have long-term-support (LTS). The cycle was released on 2021-09-28 and its latest release date was 2021-09-28.
Risk description
Using end-of-life (EOL) software poses significant security risks for organizations. EOL software no longer receives updates, including critical security patches. This creates a vulnerability landscape where known and potentially new security flaws remain unaddressed, making the software an attractive target for malicious actors. Attackers can exploit these vulnerabilities to gain unauthorized access, disrupt services, or steal sensitive data. Moreover, without updates, compatibility issues arise with newer technologies, leading to operational inefficiencies and increased potential for system failures. Additionally, regulatory and compliance risks accompany the use of EOL software. Many industries have strict data protection regulations that require up-to-date software to ensure the highest security standards. Non-compliance can result in hefty fines and legal consequences. Organizations also risk damaging their reputation if a breach occurs due to outdated software, eroding customer trust and potentially leading to a loss of business. Therefore, continuing to use EOL software undermines both security posture and business integrity, necessitating timely upgrades and proactive risk management strategies.
Recommendation
To mitigate the risks associated with end-of-life (EOL) software, it's crucial to take proactive steps. Start by identifying any EOL software currently in use within your organization. Once identified, prioritize upgrading or replacing these applications with supported versions that receive regular updates and security patches. This not only helps close security gaps but also ensures better compatibility with newer technologies, enhancing overall system efficiency and reliability.Additionally, develop a comprehensive software lifecycle management plan. This plan should include regular audits to identify upcoming EOL dates and a schedule for timely updates or replacements. Train your IT staff and users about the importance of keeping software up to date and the risks associated with using outdated versions. By maintaining a proactive approach to software management, you can significantly reduce security risks, ensure compliance with industry regulations, and protect your organization's reputation and customer trust.
Evidence
We managed to detect a publicly accessible File Transfer Protocol (FTP) service. PORT STATE SERVICE VERSION 21/tcp open ftp ProFTPD
Vulnerability description
We found that the File Transfer Protocol (FTP) service is publicly accessible. The FTP enables client systems to connect to upload and download files. Nonetheless, FTP lacks encryption for the data exchanged between the server and the client, leaving all transferred data exposed in plaintext.
Risk description
Exposing this service online can enable attackers to execute man-in-the-middle attacks, capturing sensitive user credentials and the contents of files because FTP operates without encryption. The entirety of the communication between the client and the server remains unsecured in plaintext. This acquired information could further facilitate additional attacks within the network.
Recommendation
We recommend turning off FTP access over the Internet and instead using a Virtual Private Network (VPN) that mandates two-factor authentication (2FA). If the FTP service is essential for business purposes, we recommend limiting access only from designated IP addresses using a firewall. Furthermore, utilizing SFTP (Secure File Transfer Protocol) is recommended as this protocol employs encryption to secure data transfers.
Evidence
We managed to detect a publicly accessible Post Office Protocol (POP3) service. Starting Nmap ( https://nmap.org ) at 2025-07-17 11:27 EEST Nmap scan report for club.vladimirzakharov.com (77.72.134.146) Host is up (0.015s latency). rDNS record for 77.72.134.146: masteryacademy.ru
PORT STATE SERVICE VERSION 995/tcp open ssl/pop3 Dovecot pop3d |_pop3-capabilities: CAPA RESP-CODES USER UIDL PIPELINING AUTH-RESP-CODE TOP SASL(PLAIN LOGIN CRAM-MD5)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 13.44 seconds
Vulnerability description
We found that the Post Office Protocol (POP3) service is publicly accessible and doesn’t include STARTTLS capability. Email clients use the Post Office Protocol (POP) to download emails for user accounts. Some POP servers are initially set up to operate over an unsecured protocol. When email clients download email content through this plaintext protocol, it can pose a substantial risk to the organization's network, especially depending on which user account is set to receive the emails.
Risk description
Exposing this service online can enable attackers to conduct man-in-the-middle attacks, thereby gaining access to sensitive user credentials and the contents of emails. Given that POP3 operates via a plaintext protocol, the entirety of the data exchanged between the client and server is left unencrypted. This critical information could then be leveraged in further attacks on the organization's network.
Recommendation
We recommend turning off POP3 access over the Internet and instead using a Virtual Private Network (VPN) that mandates two-factor authentication (2FA). If the POP3 service is essential for business purposes, we recommend limiting access only from designated IP addresses using a firewall. Furthermore, activating STARTTLS capability (switching the connection to a secure communication) or utilizing Secure POP3 (POP3S) is recommended, as this protocol employs encryption.
Evidence
We managed to detect that Exim smtpd has reached the End-of-Life (EOL).
Version detected: 4.95 End-of-life date: 2022-06-25 Latest version for the cycle: 4.95 This release cycle (4.95) doesn't have long-term-support (LTS). The cycle was released on 2021-09-28 and its latest release date was 2021-09-28.
Risk description
Using end-of-life (EOL) software poses significant security risks for organizations. EOL software no longer receives updates, including critical security patches. This creates a vulnerability landscape where known and potentially new security flaws remain unaddressed, making the software an attractive target for malicious actors. Attackers can exploit these vulnerabilities to gain unauthorized access, disrupt services, or steal sensitive data. Moreover, without updates, compatibility issues arise with newer technologies, leading to operational inefficiencies and increased potential for system failures. Additionally, regulatory and compliance risks accompany the use of EOL software. Many industries have strict data protection regulations that require up-to-date software to ensure the highest security standards. Non-compliance can result in hefty fines and legal consequences. Organizations also risk damaging their reputation if a breach occurs due to outdated software, eroding customer trust and potentially leading to a loss of business. Therefore, continuing to use EOL software undermines both security posture and business integrity, necessitating timely upgrades and proactive risk management strategies.
Recommendation
To mitigate the risks associated with end-of-life (EOL) software, it's crucial to take proactive steps. Start by identifying any EOL software currently in use within your organization. Once identified, prioritize upgrading or replacing these applications with supported versions that receive regular updates and security patches. This not only helps close security gaps but also ensures better compatibility with newer technologies, enhancing overall system efficiency and reliability.Additionally, develop a comprehensive software lifecycle management plan. This plan should include regular audits to identify upcoming EOL dates and a schedule for timely updates or replacements. Train your IT staff and users about the importance of keeping software up to date and the risks associated with using outdated versions. By maintaining a proactive approach to software management, you can significantly reduce security risks, ensure compliance with industry regulations, and protect your organization's reputation and customer trust.
Evidence
| Software / Version | Category |
|---|---|
| WordPress 4.9.15 | CMS, Blogs |
| MySQL | Databases |
| PHP | Programming languages |
| Ubuntu | Operating systems |
| Apache HTTP Server 2.4.52 | Web servers |
| wpBakery | Page builders, WordPress plugins |
| WooCommerce 3.4.8 | Ecommerce, WordPress plugins |
| TablePress | WordPress plugins |
| Yandex.Metrika | Analytics |
| Modernizr | JavaScript libraries |
| jQuery Migrate 1.4.1 | JavaScript libraries |
| jQuery | JavaScript libraries |
| Infinite Scroll 1.1 | JavaScript libraries |
| Google Tag Manager | Tag managers |
| Google Analytics | Analytics |
| Facebook Pixel 2.9.216 | Analytics |
| HSTS | Security |
| Google Font API | Font scripts |
| Font Awesome | Font scripts |
| RSS | Miscellaneous |
| Open Graph | Miscellaneous |
Vulnerability description
We noticed that server software and technology details are exposed, potentially aiding attackers in tailoring specific exploits against identified systems and versions.
Risk description
The risk is that an attacker could use this information to mount specific attacks against the identified software type and version.
Recommendation
We recommend you to eliminate the information which permits the identification of software platform, technology, server and operating system: HTTP server headers, HTML meta information, etc.
Evidence
| Domain Queried | DNS Record Type | Description | Value |
|---|---|---|---|
| club.vladimirzakharov.com | A | IPv4 address | 77.72.134.146 |
Risk description
An initial step for an attacker aiming to learn about an organization involves conducting searches on its domain names to uncover DNS records associated with the organization. This strategy aims to amass comprehensive insights into the target domain, enabling the attacker to outline the organization's external digital landscape. This gathered intelligence may subsequently serve as a foundation for launching attacks, including those based on social engineering techniques. DNS records pointing to services or servers that are no longer in use can provide an attacker with an easy entry point into the network.
Recommendation
We recommend reviewing all DNS records associated with the domain and identifying and removing unused or obsolete records.
Evidence
| Operating System | Accuracy |
|---|---|
| Linux 5.4 | 100% |
Vulnerability description
OS Detection